In today's high-stakes regulatory landscape—encompassing SOX, DORA, PCI DSS, and HIPAA—monitoring privileged access is a must, not a maybe. HashiCorp Boundary offers robust identity-based access control, session brokering, and detailed session recordings. But security operations centers (SOCs) need more than videos; they need structured, real-time data to fuel detection rules and alerts. By pairing Boundary's session recordings with Elastic's Auditbeat for kernel-level event capture, organizations can close the gap between forensic depth and automated detection. Here are 10 essential insights to implement this powerful combination.
1. Understanding the Two-Layer Defense
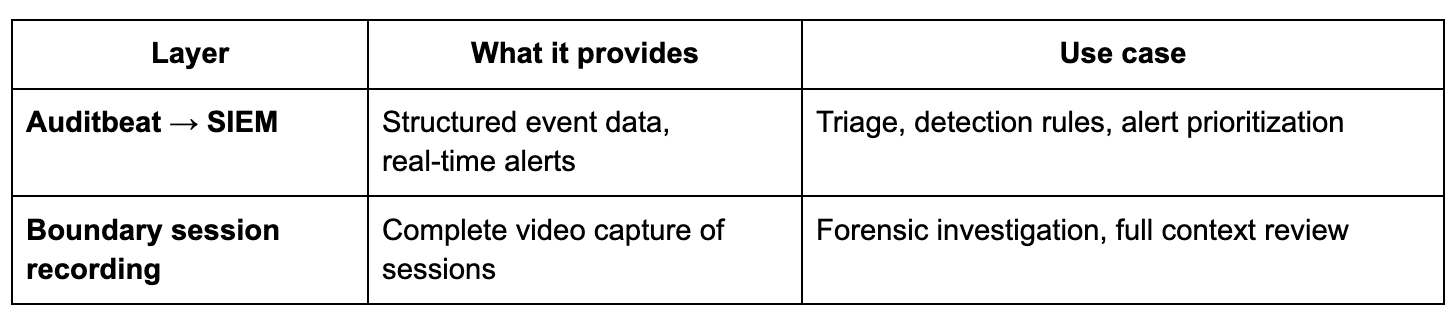
Effective privileged access monitoring requires both real-time alerting and deep forensic investigation. Boundary's session recordings provide a complete visual replay of every keystroke, command, and response—ideal for post-incident reviews. However, SOCs don't start investigations by watching videos; they start with alerts. Auditbeat supplies kernel-level audit events that feed directly into SIEM platforms, enabling automatic triggers for suspicious actions like sensitive file access or privilege escalation. This two-layer approach combines speed (alerts) with depth (recordings), ensuring no threat goes unnoticed while giving analysts the context they need for rapid response.
2. The Core Challenge: Video vs. Structured Data
Boundary's session recordings are incredibly detailed, but they're video files—not searchable text. When a privileged user connects to a production server, executes dangerous commands, and then exits, the recording holds critical evidence. Yet without structured event data, that evidence stays hidden from automated detection systems. SOCs rely on real-time alerts to triage incidents, not on manually scanning videos. The disconnect means high-risk behaviors may be missed until it's too late. By overlaying Auditbeat's structured logs on top of video evidence, organizations can ensure that every suspicious action generates an alert, bridging the gap between visibility and usability.
3. Why Kernel-Level Auditing Solves the Problem
Attempting to parse video session recordings into structured text is brittle and unreliable due to the complexity of terminal data streams. Instead, Auditbeat captures audit events directly at the operating system kernel on target hosts. This provides a clean, system-level view of every file access, process launch, and network connection—regardless of how the user connects. Because Auditbeat integrates natively with Elasticsearch and Kibana, its logs flow seamlessly into SIEMs, triggering alerts on specific patterns like multiple failed sudo attempts or access to /etc/shadow. This approach is production-ready, scalable, and far more dependable than text extraction from video.
4. Aligning with Regulatory Audit Trails
Regulations like SOX, PCI DSS, and HIPAA demand detailed audit trails for privileged access. Boundary's session recordings satisfy forensic requirements by showing exactly what happened. Auditbeat compliments this by logging every kernel event with precise timestamps and user IDs. Together, they create an unbroken chain of evidence: the structured log says “who did what when” and the recording shows “how they did it.” This combination not only meets compliance mandates but also streamlines auditor reviews—providing both a summary report and video proof without extra manual effort.
5. Real-Time Detection of Risky Behaviors
With Auditbeat feeding data into your SIEM, you can write detection rules for privileged session activities. For example, if a user reads /etc/shadow, attempts privilege escalation via sudo, and launches network reconnaissance tools, each action triggers an instantaneous alert. This allows SOC analysts to investigate while the session is still active or shortly after it ends. Boundary's session recording is then pulled up for visual confirmation, verifying the user's exact keystrokes and system responses. This real-time correlation reduces dwell time and helps contain breaches before they escalate.
6. Seamless Integration with Existing SIEM Tools
Auditbeat is part of the Elastic Stack, making it a natural fit for organizations already using Elasticsearch, Logstash, and Kibana. However, its structured output (JSON) can be ingested by any SIEM platform, including Splunk, QRadar, or Azure Sentinel. Boundary can be configured to send session metadata (e.g., start time, user, target host) to the same SIEM via webhooks or syslog. This unified data lake means security analysts can query both the structured logs and the associated session recordings from a single console, simplifying investigations and reducing context-switching.
7. Reducing False Positives with Visual Context
Structured logs alone can generate noise—a file access alert might be routine maintenance. When Auditbeat triggers an alert, analysts can immediately view the corresponding Boundary session recording. Seeing the full terminal interaction helps distinguish between malicious intent and a legitimate admin task. For instance, accessing /etc/shadow to verify a configuration is different from copying it for exfiltration. This visual context cuts false positives, improves alert fidelity, and allows security teams to focus on genuine threats without drowning in alerts.
8. Scaling Across Hybrid and Multi-Cloud Environments
Boundary and Auditbeat are both designed for distributed deployments. Boundary brokers access to resources across on-premises, cloud, and hybrid environments. Auditbeat agents can be installed on any Linux or Windows host (and soon macOS) to capture kernel events regardless of location. This scalability ensures that privileged activity on servers in AWS, Azure, or a private data center is uniformly logged and monitored. Centralized policy management via Boundary and Auditbeat's configuration management integration (e.g., with Ansible or Terraform) makes deployment and maintenance straightforward as your infrastructure grows.
9. Enhancing Incident Investigation Efficiency
When a major incident occurs, time is critical. Instead of manually correlating logs from multiple sources, analysts can pivot directly from an Auditbeat alert to the associated Boundary session recording. Elastic's integration allows embedding direct links to recordings in SIEM alerts. During a post-incident review, the structured log provides a timeline of events, while the recording offers a frame-by-frame breakdown. This synergy reduces investigation time from hours to minutes, enabling faster containment, root cause analysis, and reporting to stakeholders or regulators.
10. Future-Proofing Your Privileged Access Strategy
As threats evolve, so must monitoring capabilities. Boundary continues to enhance its session recording features, including seeking support for richer metadata and API extensions. Auditbeat is constantly updated to capture new system events and improve performance. By adopting this two-layer approach today, organizations build a foundation that adapts to emerging risks—whether that's monitoring containerized workloads, integrating with AI-driven detection engines, or meeting new compliance requirements. Starting with Boundary + Auditbeat positions your security operations for long-term resilience and agility.
In summary, combining HashiCorp Boundary's session recordings with Elastic's Auditbeat creates an unbeatable duo for privileged access monitoring. You gain the real-time, structured alerts that SOCs need to detect threats fast, plus the full forensic videos required for deep investigation. This layered strategy not only satisfies regulatory demands but also empowers security teams to stay ahead of adversaries. Implement these 10 steps to transform your threat detection from reactive to proactive, and ensure every privileged session leaves a trail—both in text and in video—that is searchable, alertable, and actionable.